Information Security Risk Management Framework

Information Security Policy
(I) Purpose
To maintain the Company's overall information security environment, to
strengthen the security management of various information assets, and to
establish a convenient and safe electronic work environment for the purpose
of ensuring the security of data, systems, equipment and networks.
(II) Scope
The Company's scope of information security management includes thevarious information assets (including software and hardware equipment) ofthe Company and the information users, such as permanent employees,temporary employees, contract employees, external vendors and otherpersons authorized to use the information assets.
(III) Information Security Goals
It comprehensively considers the importance and the value of each information asset and the extent to which it affects and harms the Company's business, resulting from the improper use of the Company's information properties, data leakage, malicious tampering, damage, etc., due to risks of human negligence, intentional or natural disasters and others so that it adopts the security measures of management, operation and technology which are commensurate with the value of information assets and cost-effective, i The Company is able to avoid improper use or deliberate destruction of information systems by internal and external personnel or it can respond quickly to reduce the economic damage and operation interruption that maybe caused by information security incidents when information security incidents occur.
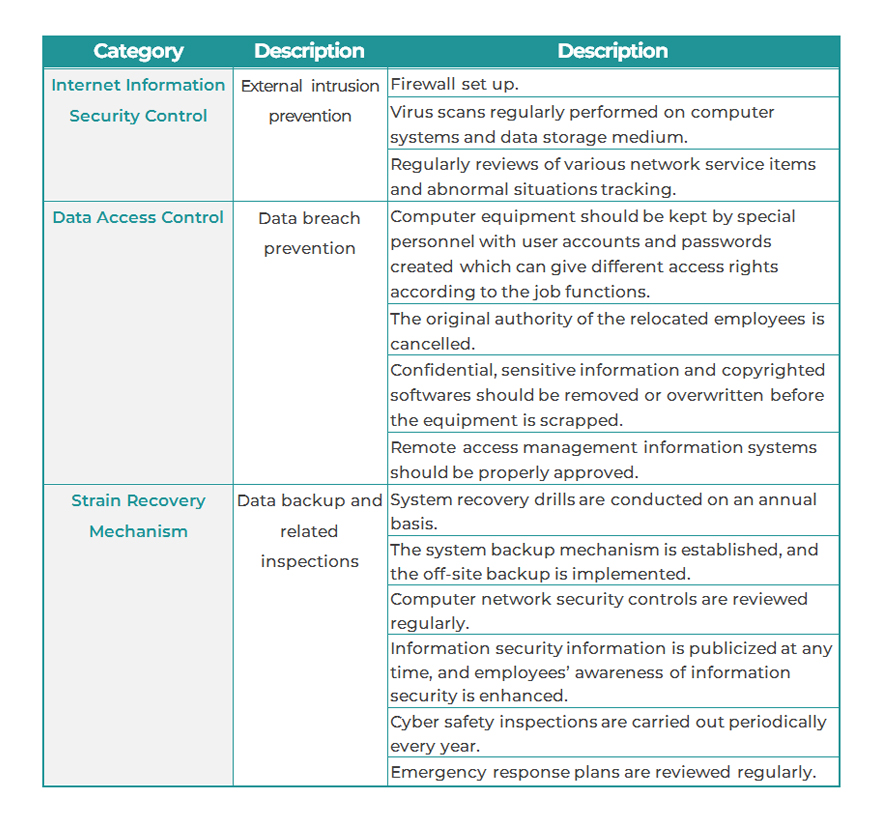
(IV) Information Security Management Measures
- Personal information should be handled prudently in accordance with the Personal Data Protection Act.
- Passwords should be created, anti-virus softwares should be installed ,and virus patterns should be updated regularly to both personal computers and servers.
- Personal computer equipment should also be managed to ensure that the software installed is legally authorized to comply with relevant regulations on intellectual property right.
- Important data should be backing up, and the backup validity of the data should be checked regularly.
- Disaster recovery plans should be planned to quickly restore system operations in the event of information security incidents.
- Information security awareness campaigns should be carried out on a regular basis and the colleagues' information security awareness and legal concept should be strengthened.
Specific Management Plans
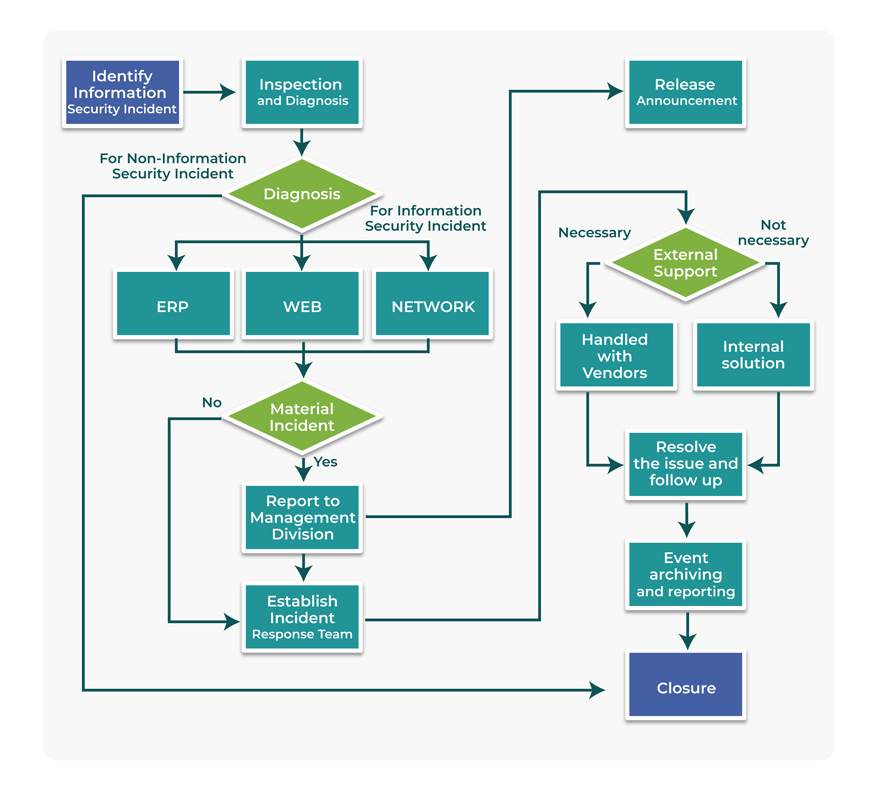
Information Security Incident Reporting Procedures
Information Security Management Resource Investment
The Company continues to invest resources in information security and personal data protection related matters, and the matters of the resource investment include to improve the security infrastructure of governance and technology and to strengthen information security defense equipment and education and training, etc.
The Company also timely updates information security protection equipment, such as firewall, IPS, anti-virus, etc. to optimize the protection effect in response to the frequent occurrence of information security incidents in private enterprises and public sectors in recent years. The security of the information system is updated regularly, and the Company's material information systems are preformed for vulnerability assessment and patching vulnerabilities every year.
To enhance the information security awareness of our employees, meetings, bulletin boards, and corporate internal websites are used to publicize information security awareness to our colleagues, and suspicious data and emails, if any, should not be opened carelessly to avoid social engineering attacks.
